Securing RDP: Best Practices for Protecting Your Remote Desktop
In our digital age, online businesses with remote employees are becoming increasingly common. More people are becoming digital nomads or choosing to work remotely. This growing trend makes securing remote desktop connections more critical than ever. With the widespread use of Remote Desktop Protocol (RDP), it is essential to take security measures seriously to protect sensitive data. But you might wonder, is RDP secure? If not, can it be made secure with the right practices?
What Is RDP?
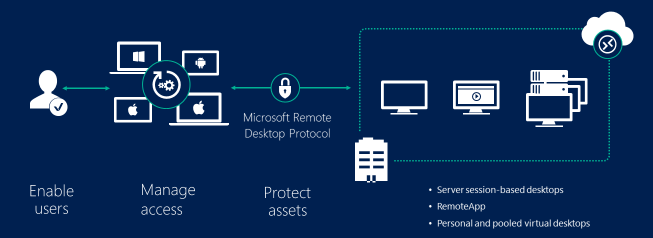
Remote Desktop Protocol (RDP) is a proprietary protocol developed by Microsoft, allowing users to connect to another computer over a network connection. It provides a graphical interface, enabling users to access the desktop and applications of a remote machine as if they were physically present.
Is RDP Secure?
RDP is widely used but comes with security concerns that need to be addressed to prevent unauthorized access and data breaches.
Encryption in RDP
RDP supports 128-bit encryption to protect the data transferred between the client and server. However, the default encryption settings may not be robust enough for all environments, so it’s important to configure RDP for enhanced security.
Common RDP Vulnerabilities
Several vulnerabilities can compromise RDP security:
- Weak Passwords: Using weak or default passwords makes it easy for attackers to gain access.
- Open RDP Ports: Exposing RDP ports to the internet can lead to brute force and denial-of-service attacks.
- Lack of Multi-Factor Authentication: Without 2FA, unauthorized access is more likely if credentials are compromised.
- Unpatched Systems: Not applying security updates leaves systems vulnerable to known exploits.
How to Secure RDP?
To secure RDP, follow these best practices:
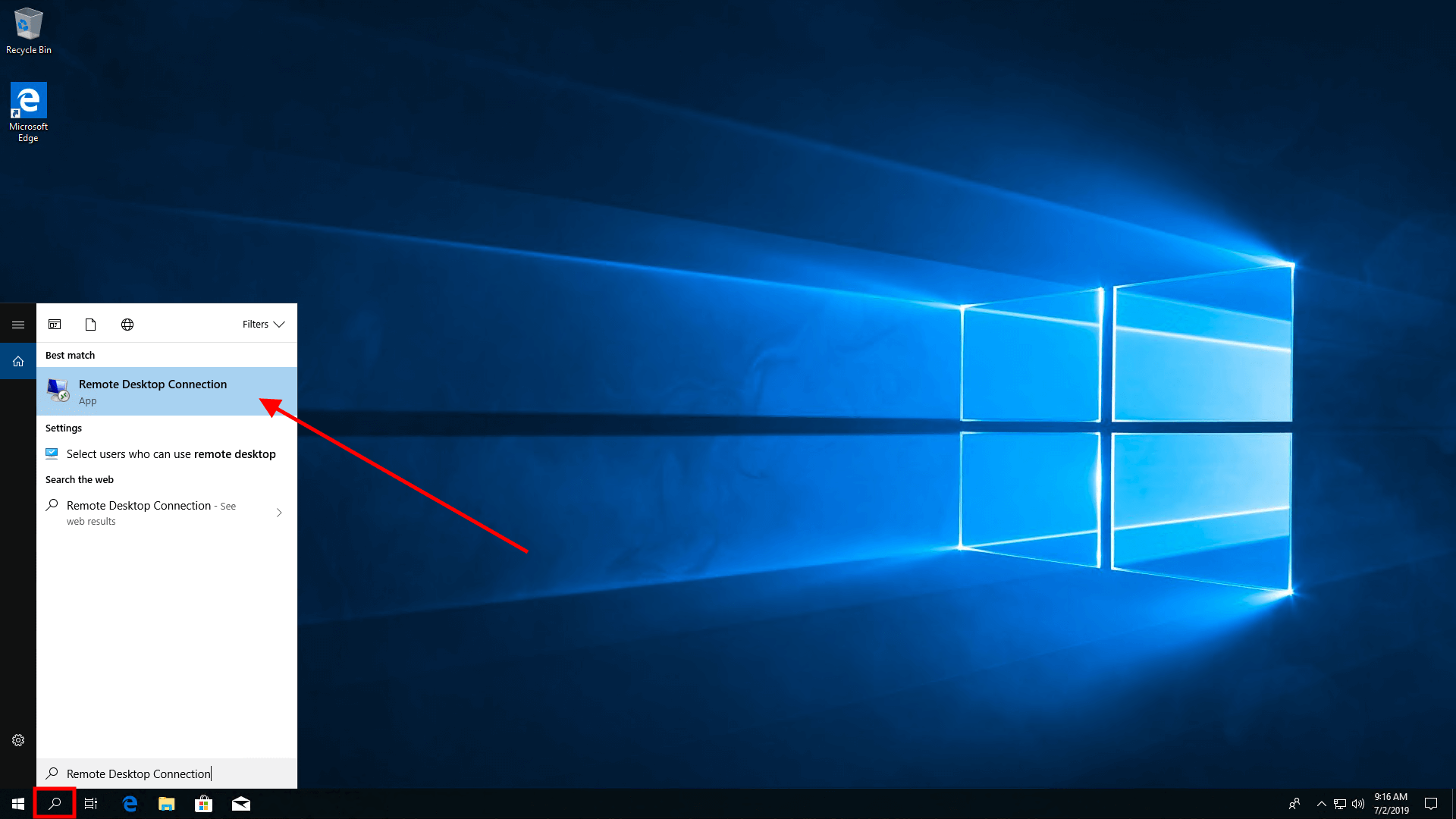
Enable Network Level Authentication (NLA)
NLA requires users to authenticate before establishing a full RDP session, providing an additional layer of security. To enable NLA:
1. Open the System Properties dialog box.
2. Click the Remote tab.
3. Under Remote Desktop, select "Allow connections only from computers running Remote Desktop with Network Level Authentication."
Implement Two-Factor Authentication (2FA)
Two-Factor Authentication adds an extra layer of security by requiring a second form of verification. Tools like Duo Security can integrate 2FA with RDP.
Restrict RDP Access
Limit RDP access to specific users and groups, and disable it for those who do not need it. To restrict access:
1. Open Local Group Policy Editor.
2. Navigate to Computer Configuration > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Connections.
3. Configure "Allow users to connect remotely by using Remote Desktop Services."
Apply Windows Updates
Regularly update your Windows systems to ensure all security patches are applied. You can configure automatic updates through the Windows Update settings.
Use VPNs for Secure Remote Connections
Using a VPN provides an encrypted tunnel for your RDP sessions, adding an extra layer of security. Ensure your VPN is configured correctly and that all users connect through it.
Whitelist IP Addresses
Restrict RDP access to only trusted IP addresses by configuring your firewall or router. This minimizes the risk of unauthorized access from unknown sources.
To configure a Windows Firewall rule:
1. Open Windows Defender Firewall with Advanced Security.
2. Click Inbound Rules > New Rule.
3. Select Custom, then Next.
4. Specify the IP addresses to allow, then finish the rule setup.
Additional RDP Security Measures
Consider these additional measures to further enhance RDP security:
Audit Logs
Enable audit logs to monitor RDP access and activities. This helps in identifying and responding to suspicious activities.
1. Open Local Group Policy Editor.
2. Navigate to Computer Configuration > Windows Settings > Security Settings > Advanced Audit Policy Configuration.
3. Configure auditing for logon events.
Account Lockout Policies
Configure account lockout policies to prevent brute force attacks by locking out accounts after a number of failed login attempts.
1. Open Local Group Policy Editor.
2. Navigate to Computer Configuration > Windows Settings > Security Settings > Account Policies > Account Lockout Policy.
3. Set the desired values for lockout threshold and duration.
Session Timeout Settings
Set session timeouts to automatically log off idle sessions, reducing the risk of unauthorized access if a session is left open.
1. Open Local Group Policy Editor.
2. Navigate to Computer Configuration > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Session Time Limits.
3. Configure session time limits.
Disable Clipboard Redirection
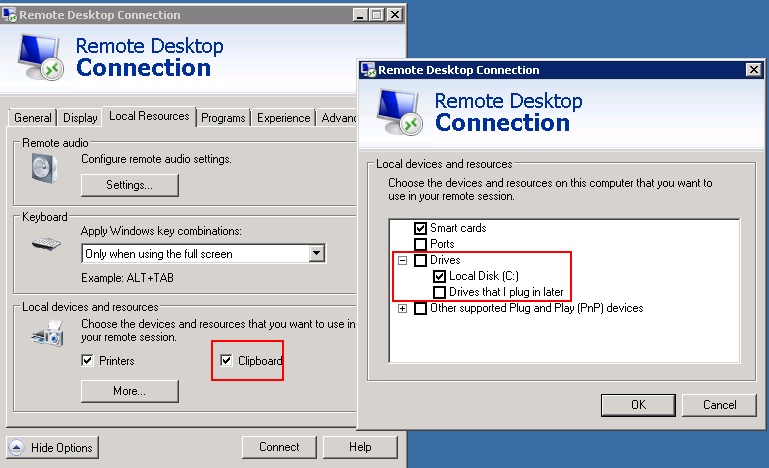
Disable clipboard redirection to prevent data leakage between the local and remote systems. This can be configured through Group Policy:
1. Open Local Group Policy Editor.
2. Navigate to Computer Configuration > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Device and Resource Redirection.
3. Disable "Do not allow clipboard redirection."
Use DP Gateways
Using an RDP Gateway is highly recommended as it provides a secure way to restrict access to Remote Desktop ports while supporting remote connections through a single gateway server. With an RD Gateway server, all Remote Desktop services on your desktops and workstations should be configured to only allow access from the RD Gateway. The RD Gateway server listens for Remote Desktop requests over HTTPS (port 443) and connects the client to the Remote Desktop service on the target machine.
- Utilize Campus RDP Gateway Service: This is the best option for allowing RDP access to systems categorized as UC P2 and lower, and it includes DUO integration. The RDP Gateway Service is provided by the Windows Team. Documentation is available here.
- Compliance with Remote Access Services Requirement: The RDP Gateway Service supports the new Remote Access Services requirement of the draft MSSND update (requirement 8), which mandates the use of an approved service (e.g., RDP gateway, dedicated gateway, or bSecure VPN) for accessing the UC Berkeley network from the public Internet.
- Dedicated Gateway Service (Managed): Required for RDP access to systems categorized as UC P4 or higher and must be configured for DUO. Some campus units use a Berkeley IT managed VPS as an RD Gateway, supporting an estimated 30-100 concurrent users. High Availability (HA) at the virtual layer ensures fault-tolerant and reliable access, with the option for network load balancing for more sophisticated implementations.
- Dedicated Gateway Service (Unmanaged): Involves installing and configuring the RD Gateway on department-run hardware. Numerous online documents are available for configuring this component in Windows 2016/2019. Official documentation can be found here.
- Certificates: While a self-signed certificate is acceptable for testing, using a Calnet-issued trusted Comodo certificate is recommended for production. A CalnetPKI certificate can also work if all clients trust the UCB root, but a Comodo certificate is generally better accepted to avoid certificate warnings for end users.
- Client Configuration: Configuring your client to use your RD Gateway is straightforward. The official documentation for the MS Client is available here. Essentially, you only need to make a simple change on the advanced tab of your RDP client.
By using an RDP Gateway, you can ensure a higher level of security for your Remote Desktop connections, protecting sensitive data and maintaining compliance with security requirements.
Connect to RDP Server with SSH
Using SSH tunneling for RDP adds an extra layer of security by encrypting the RDP traffic. If using an RD Gateway is not feasible, you can enhance security by tunneling your Remote Desktop sessions through IPSec or SSH, adding an extra layer of authentication and encryption. IPSec is built into all Windows operating systems since Windows 2000, with significant improvements in usability and management in Windows 10 (see: Microsoft Technet). Alternatively, if an SSH server is available, you can use SSH tunneling for your Remote Desktop connections.


This article incorporates information and material from various online sources. We acknowledge and appreciate the work of all original authors, publishers, and websites. While every effort has been made to appropriately credit the source material, any unintentional oversight or omission does not constitute a copyright infringement. All trademarks, logos, and images mentioned are the property of their respective owners. If you believe that any content used in this article infringes upon your copyright, please contact us immediately for review and prompt action.
This article is intended for informational and educational purposes only and does not infringe on the rights of the copyright owners. If any copyrighted material has been used without proper credit or in violation of copyright laws, it is unintentional and we will rectify it promptly upon notification. Please note that the republishing, redistribution, or reproduction of part or all of the contents in any form is prohibited without express written permission from the author and website owner. For permissions or further inquiries, please contact us.


