Russians Hacked: a MITM (Man-In-The-Middle) Attack on the Jabber (XMPP) Service Within the Hosting Networks of Hetzner and Linode.
On October 20, 2023, the jabber.ru (xmpp.ru) administrator reported the detection of a man-in-the-middle (MITM) attack aimed at decrypting user traffic that had been conducted over several months on the networks of German hosting providers Hetzner and Linode. These IT resources host the project’s server and auxiliary VPS environments. The attack was orchestrated by redirecting traffic to a transit node that substituted the TLS certificate for XMPP connections encrypted using the STARTTLS extension.
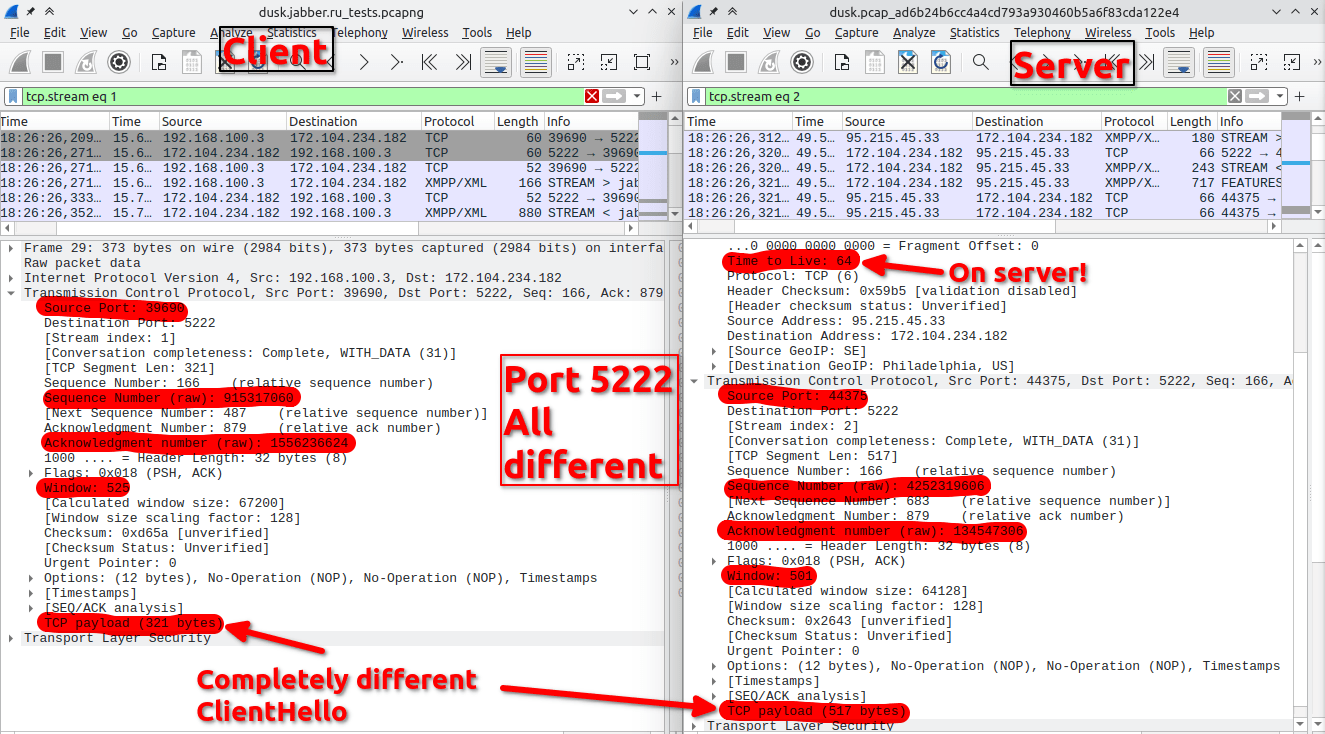
Unknown participants of this attack issued a separate SSL certificate and proxied connections to TCP port 5222.
The attack was discovered due to a mistake made by its organizers, who failed to renew the TLS certificate used for substitution.
On October 16, while trying to connect to the service, the administrator of jabber.ru received an error message due to the expiration of the certificate. However, the certificate hosted on the server had not expired. As a result, it was revealed that the certificate received by the client differed from the certificate sent by the server.

The first fake TLS certificate was obtained on April 18, 2023, through the Let’s Encrypt service, where the attacker, having the ability to intercept traffic, was able to confirm access to the jabber.ru and xmpp.ru websites.
At first, the administration of jabber.ru suspected a compromise of the project’s server and a substitution carried out on its side. However, the conducted audit did not reveal any signs of hacking. At the same time, a brief network interface card (NIC) link down/up was noticed in the server log, which occurred on July 18 at 12:58 and could indicate manipulations with the server’s connection to the switch. Notably, two fake TLS certificates were generated just minutes before that – on July 18 at 12:49 and 12:38.
Moreover, the substitution was not only carried out in the network of the Hetzner provider, where the main server was located, but also in the network of the Linode provider, which hosted VPS environments with auxiliary proxies redirecting traffic from other addresses. Indirectly, it was found out that the traffic on network port 5222 (XMPP STARTTLS) in the networks of both providers was redirected through an additional host, which gave reason to believe that the attack was carried out by someone with access to the providers’ infrastructure.
Theoretically, the substitution could have been carried out since April 18 (the date of creation of the first fake certificate for jabber.ru), but confirmed cases of certificate substitution were only recorded from July 21 to October 19. Therefore, all this time, the encrypted data exchange with jabber.ru and xmpp.ru can be considered compromised.
The certificate substitution ceased after the investigation began, tests were conducted, and a request was sent to the support services of the Hetzner and Linode providers on October 18. However, an additional transition in the routing of packets sent to port 5222 of one of the servers in Linode is still observed, but the certificate is no longer being substituted.
The project team assumes that the attack could have been carried out with the knowledge of the providers at the request of law enforcement agencies, as a result of hacking the infrastructure of both providers, or by an employee who had access to both providers. Having the ability to intercept and modify XMPP traffic, the attacker could have accessed all data associated with accounts, such as the history of message exchanges stored on the server, as well as send messages on behalf of others and make changes to others’ messages. Messages sent using end-to-end encryption (OMEMO, OTR, or PGP) can be considered uncompromised if the encryption keys have been verified by users on both sides of the connection.
Users of jabber.ru are advised to change their access passwords and check the OMEMO and PGP keys in their PEP storages for possible substitution.
Source: https://habr.com/ru/news/768914/

This article incorporates information and material from various online sources. We acknowledge and appreciate the work of all original authors, publishers, and websites. While every effort has been made to appropriately credit the source material, any unintentional oversight or omission does not constitute a copyright infringement. All trademarks, logos, and images mentioned are the property of their respective owners. If you believe that any content used in this article infringes upon your copyright, please contact us immediately for review and prompt action.
This article is intended for informational and educational purposes only and does not infringe on the rights of the copyright owners. If any copyrighted material has been used without proper credit or in violation of copyright laws, it is unintentional and we will rectify it promptly upon notification. Please note that the republishing, redistribution, or reproduction of part or all of the contents in any form is prohibited without express written permission from the author and website owner. For permissions or further inquiries, please contact us.


